The Top 10 Most Notorious Hackers in the World.

Kevin David Mitnick – American hacker and author. Born on August 6, 1963. He was best known in Hacking spree of national defense warning system and other corporate top secret information. He’s other names are “The Condor”, “The Darkside Hacker”.
https://www.makeuseof.com/tag/5-of-the-worlds-most-famous-hackers-what-happened-to-them/; https://en.wikipedia.org/wiki/Kevin_Mitnic; https://www.raisethebar.co.uk/speaker/kevin-mitnick/

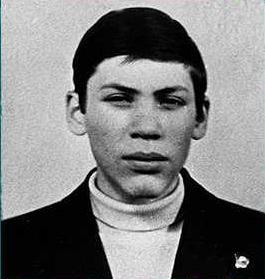
Jonathan James – American hacker. Born on December 12, 1983. He was the first juvenile to be imprisoned because of commiting cybercrime. He was only 15 years old at that time of imprisonment. At 15 years old, He hacked companies, schools, Department of Defense and NASA. He used the pseudonym “Comrade”.
https://techasli.com/story-jonathan-james-hacked-nasa-pentagon-age-15/ ; https://www.makeuseof.com/tag/5-of-the-worlds-most-famous-hackers-what-happened-to-them/ ; https://tophackers.wordpress.com/9-c0mrade/
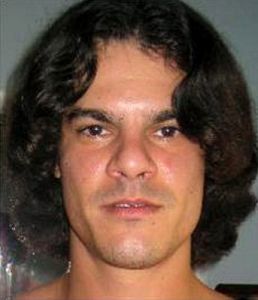
Albert Gonzalez – American Hacker. Born on the year 1981. He was accused of the biggest fraud in history. He mastermind the credit card theft, selling 170 million card, ATM numbers. He was sentenced 20 years in prison.
https://www.makeuseof.com/tag/5-of-the-worlds-most-famous-hackers-what-happened-to-them/; https://en.wikipedia.org/wiki/Albert_Gonzalez; https://en.wikipedia.org/wiki/Albert_Gonzalez#/media/File:Albert-gonzalez.jpg

Kevin Poulsen – American Hacker. Born on November 30, 1965. He was famous in hacking the telephone lines of a radio station and making him as the winning caller where the prize is a brand new Porche. He is also known as the “ Dark Dante”. After he was captured, he was sentence to 51 months of imprisonment and a fine of $56,000.
https://en.wikipedia.org/wiki/Kevin_Poulsen; https://en.wikipedia.org/wiki/Kevin_Poulsen; https://en.wikipedia.org/wiki/Kevin_Poulsen#/media/File:Kevin_Poulsen_2014.png

Gary McKinnnon – A British Hacker. Born on February 10, 1966. He was famous in penetrating the computers of US Armed Forces and NASA. His aim is to search for the information on free energy suppression and some UFO information. He made some of the computers unusable amounting the damage in $700,000 .
https://en.wikipedia.org/wiki/Gary_McKinnon;; https://www.makeuseof.com/tag/5-of-the-worlds-most-famous-hackers-what-happened-to-them/; https://www.wired.com/2012/10/mckinnon-extradition-win/

Robert Tappan Morris – An American computer scientist. Born on November 8, 1965. He was famous in creating the first computer worm and it is called “Morris Worm”. His computer worm infected over 6,000 computers making them usable because the worm infected computer can be infected multiple times making the performance of the computer to degrade. In 1989, He was found guilty in violating the Computer Fraud and Abuse Act. His sentence was three years in probation, $10,050 fine and 400 hours community service.
https://www.makeuseof.com/tag/5-of-the-worlds-most-famous-hackers-what-happened-to-them/; https://www.google.com/search?client=firefox-b-ab&q=Robert+Tappan+Morris; https://en.wikipedia.org/wiki/Robert_Tappan_Morris

Loyd Blankenship – An American hacker. Born on the year 1965. He also called by the name of “The Mentor”. Since 1970’s, he has been active as a hacker and a member of several hacking groups and one of the hacking groups is the Legion of Doom. He authored the essay entitled the “Hacker Manifesto”, it was written after he was arrested in 1986.
https://www.makeuseof.com/tag/5-of-the-worlds-most-famous-hackers-what-happened-to-them/; https://en.wikipedia.org/wiki/Loyd_Blankenship; https://www.soldierx.com/hdb/Mentor

Michael Calce – A Canadian hacker. Born on the year 1986. He is famously known as the “Mafia Boy”. On February 7, 2000, He successfully attack and shutdown Yahoo.com using the Distributed Denial-of-Service Attack under the project name Rivolta. Aside from Yahoo.com, there are other site that he attacks like eBay, CNN, and Amazon but he was unsuccessful shutting down Dell servers.
https://www.npr.org/sections/alltechconsidered/2015/02/07/384567322/meet-mafiaboy-the-bratty-kid-who-took-down-the-internet; https://en.wikipedia.org/wiki/MafiaBoy
Vladimir Levin – A Russian hacker. Born on the year 1967. He was famous in the involvement attempt to transfer $10.y million thru CitiBank’s computers. Back then he was known as a mathematician with a degree in biochemistry from Saint Petersburg State Institute of Technology
https://en.wikipedia.org/wiki/Vladimir_Levin; https://www.complex.com/pop-culture/2012/02/the-8-best-computer-hackers-of-all-time/5; https://4ehack.wordpress.com/2012/12/27/top-10-hackers-of-all-time/vladimir_levin/

Max Ray Butler – An American hacker. Born on July 10, 1972. He was the perpetrator who is involved in million dollar credit card scheme, stealing 1.8 million credit card numbers. He was sentenced 13 years imprisonment and a fine of $27.5 million.
https://www.complex.com/pop-culture/2012/02/the-8-best-computer-hackers-of-all-time/6; https://en.wikipedia.org/wiki/Max_Butler; https://www.wired.com/2009/06/butler-court/
Why the cost to identify and remove a defect in the early stages of the software development might be 100 times less than the cost of removing a defect in software that has been distributed to hundreds of customers?
The cost to identify and remove a defect in the early stages of the software development might be 100 times less than the cost of removing a defect in software than has been distributed to hundreds of customers. This statement is true because in software development stage no physical product is involve only the software code is involve in fixing such bugs if it is detected earlier. Compared to the situation where the software has been distributed to hundreds of customer it will cause a lot of fortune to company’s finances where it has been distributed and then if the customers finds out about the software bugs, they would request for a refund because the specified software does not perform according to what the label said. It will also reflect the image of company who produce the defective software and might the customer will not support other software product that been producing of the said company.
The three criteria that I consider to be most important in a quality system. Briefly discuss your rationale for selecting these criteria.
Customer must be in the center of the quality system.
Customer must be in the center of the quality systems because the customer will use the finish product not the developer. It must be produced according what the client’s preference and what suit it need to perform optimally using the product delivered by the developer. It must be user-friendly to be able the user to learn how to use it faster and efficiently.
Risk Management should be a part of any Quality Management.
Risk Management should always be a part of any Quality Management because not all finish product are 100 percent free from bugs and defects i should be important to be able to meet and help end user to use the product in the fastest time after the software defects occur. Each stage of the development should identify, assess, treat and monitor risks. Unlike other criteria in Quality Management System, the Risk Management should always be implemented even in after sales.
Mobility has come to be an important feature of any QM system.
Today mobility is an advantage in every aspect of business because it can make software management more efficient just by making it to the client wirelessly via remote system. Mobility of Quality Management System will help in coping up in the fast phase of the modern commerce.
https://www.bpa-solutions.net/blog/7-criteria-quality-management-system-must-meet/
